SHA256 is a cryptographic hash function, commonly used to verify data integrity, such as its use in digital signatures. Passwords are frequently hashed and saved, without needing to store a password in plaintext. This provides an extra layer of security as a hash is not ‘reversible.’ It’s a one-way function, and each hash is unique (with the exception of collisions, but that’s out-of-scope for this tutorial.)
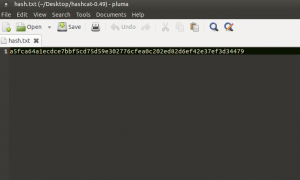
For this instance, let’s say we’re trying to recover a password (Apples123) that’s been hashed with SHA256 (a5fca64a1ecdce7bbf5cd75d59e302776cfea0c202ed82d6ef42e37ef3d34479).
We want to recover that password because we forgot it. There’s many different types of attacks we can use against a hash, namely dictionary attacks and bruteforce. Let’s say that we have a rough idea of how long the password was, and we know that there are no special characters (!@#$^*). If we wanted to run a plain bruteforce attack, this would take ages. Because of the data that we know, we are able to optimize a much more efficient attack at calculating the original value of the hash. We are able to set a custom character set, and set a specified range of possible lengths of our password.
Using a mask attack (when applicable) can significantly improve your odds at recovering the password. We can reduce the cracking time from thousands of years to a couple hours. Enter Hashcat/OclHashcat (Ocl is the CUDA/OpenCL implementation of hashcat, accelerated by a GPU to utilize it’s parallel processing ability and hundreds-to-thousands of cores.) Hashcat is also able to utilize multi-threading, in addition to certain instruction sets that are advantageous to this type of operation (Intel: AVX/2 and AMD: XOP.)
Let’s start out by grabbing a copy of Hashcat from their website here.
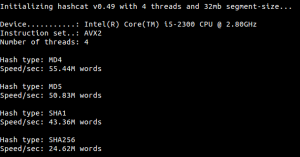
I’ll start out by running a benchmark to get a ballpark idea of how fast we can crack our hashes.
I used the following command (I chose the AVX2 binary because of my i5 processor, and you may use the standard hashcat or the XOP for AMD):
./hashcat-cliAVX2.bin -b
Using the -b option, hashcat will run a benchmark for various hashing algorithms. We’re only interested in SHA256, which comes out to about 24M attempts a second. In the real world, there are many factors that will slow us down, so realistically, we should not expect this speed.
So we have our hash, we have some limited information about our password, and have our tool ready for work. Let’s begin.
Inside the directory you extracted hashcat too, we’ll create a simple plaintext document. I’ll name it hash.txt. I’ll add our hash value calculated earlier to this text file.
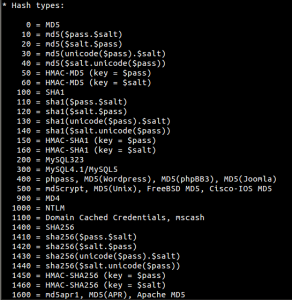
Okay, we’ve got our target hash saved, let’s get to work. Hashcat can crack dozens of different types of hashes from WPA to NTLM/LM. It can also handle salted hashes, passwords, etc… Again out of scope but relevant to know.
We’ll need to find the option for SHA256.
As you can see, we’ll be using 1400 for plain SHA256. Remember that mask attack I was talking about? That’s attack type ‘3’. We know our password starts with a capital letter, is 9 characters in length, and has 3 numeric characters. In a real world scenario, we might not know any information, but when we do, we can use it to our advantage is massively reduce the time needed to crack the hash. Here’s what our attack will look like:
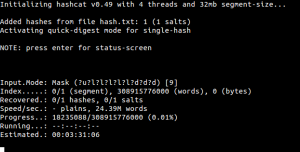
./hashcat-cliAVX2.bin -m 1400 -a 3 --pw-min 9 --pw-max 9 hash.txt -o cracked.txt "?u?l?l?l?l?l?d?d?d"
We ‘-m’ for hash type (1400 = SHA256), ‘-a’ for attack mode (3 = bruteforce/mask), –pw-min and max for our specified length, hash.txt for our hash to be cracked, ‘-o’ will output the hash when cracked to cracked.txt, and finally our mask. ?u is the character set for capital letters, ?l is lowercase letters, and ?d is numbers.
We’ve cut our time down to about three and a half hours to crack our hash. We can optimize our attack even more if you know that specific characters will be in a certain place. Let’s say a password only uses the letters ‘A-F’. We can create a custom character set by using -1 ABCDEF and then using ?1. We can also throw numbers in there too with -1 ABCDEF?d. Do you see what I’m doing here? Let’s say we want to do a second custom character set with lowercase and uppercase letters, we’d do -2 ?u?l and ?2. Since we already used -1, we’ll used -2. Now you can really see the power of this attack.
In order to save a bit of time, I optimized my character set to only use ‘pples’ (I’m cheating, but doing so to demonstrate the power of a mask attack.) The end result will look like this:
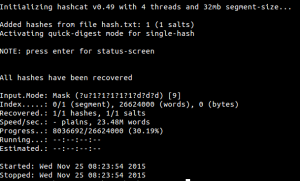
And finally, our cracked hash:
And we’re done! If we were to use a GPU like an AMD7970, we could crack this in mere minutes, as GPU cracking is magnitudes faster.
(This article will be undergoing significant improvements in the next couple of days to organize the information and present it in a better format, along with some better examples and definitions.)

Pretty! This has been an extremely wonderful article.
Thank you for providing this info.
So how would I go about adding a suffix in that? Like f-“11 characters”
Those 11 characters would consist of capital letters , letters and numbers, what do I need to add that as? since ?a would also count symbols in.
If I understand correctly, you could do something like:
-1 ?lud ?1?1?1?1?1?1?1?1?1?1?1
Where -1 = custom charset
l = lowercase
u = uppercase
d = digits
?1?1?1?1?1?1?1?1?1?1?1 = 11 possible characters using our custom charset -1
Didn’t quite get me the result I wanted.
I still need the suffix infront of the 11 possible characters.
Would this command:
Hashcat64.exe -m 1400 -a 3 hash.txt -o cracked.txt “-1 ?lud 2-?1?1?1?1?1?1?1?1?1?1?1”
This would generate a string with the prefix 2- and then 11 characters either being lower/uppercase or numbers right?
Yes, that would be correct.
-1 ?lud 2-?1?1?1?1?1?1?1?1?1?1?1
I understand what you were asking now.
I Don’t know
How to increase speed of hashcat
Because its just 177 words per second